Penetration testing
Will your company resist a hacker attack?
We'll find out the real level of your security.
WHY DO PENETRATION TESTING
The penetration test simulates a hacker attack on you. This will reveal exactly what the strengths and weaknesses of your security are.
Gone are the days when you could count on being too small and uninteresting for hackers. Today, hackers lead automated and financially motivated attacks on even the smallest companies and users.
Therefore, protect your investment in cyber security and security technologies. Verify their effectiveness by regular testing. Hackers are also not lazy and are constantly improving their tactics.
What types of penetration tests we do?
External penetration tests
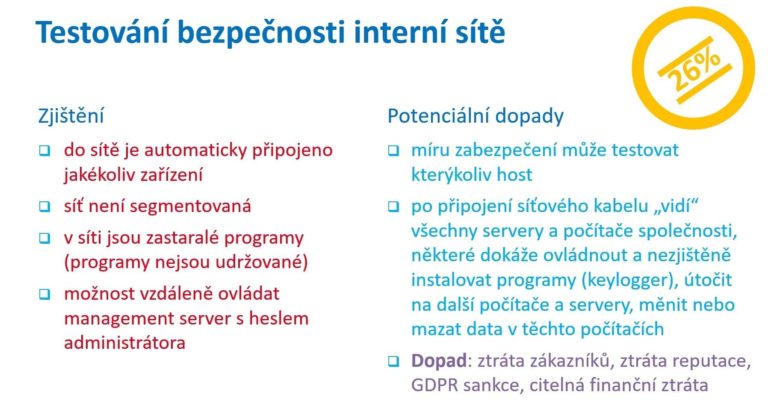
Internal penetration tests
Tests of mobile applications
Website tests
API penetration tests
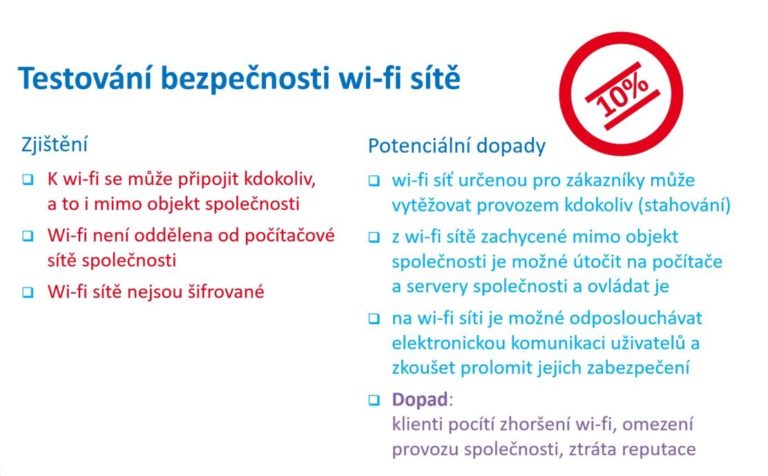
Wi-Fi penetration tests
DoS tests (stress tests)
Phishing campaigns
How does penetration testing work?
Test selection
The testing itself
Final Report
Our ethical hackers are constantly learning. They always detect all the latest hacking tactics.
What is the motivation of the attackers?
- Theft of user data
- Hosting illegal content
- Search engine SEO optimization
- Sending spam
- Spread of malware
- Rental of server capacity
How does a simulated hacker attack work?
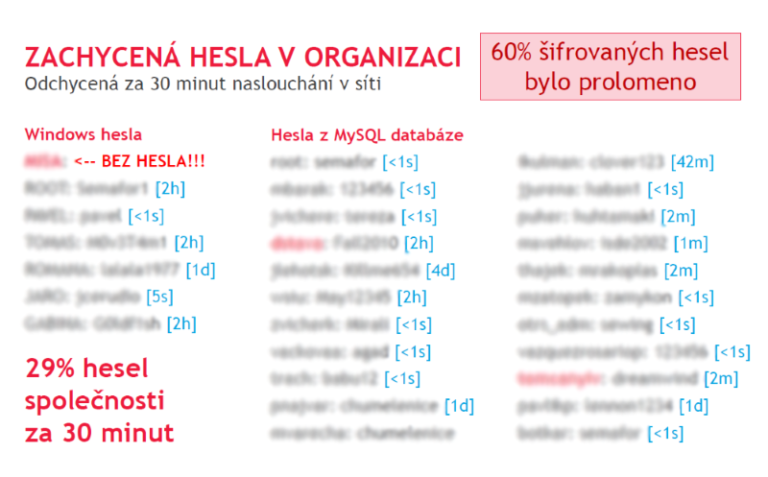
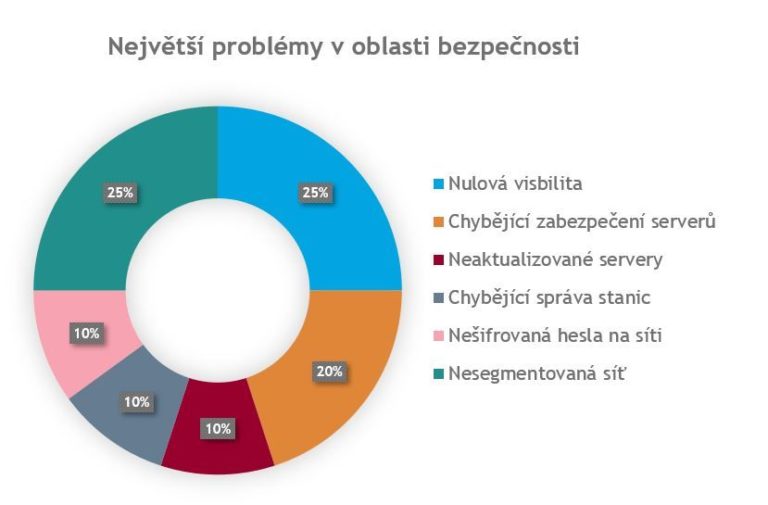
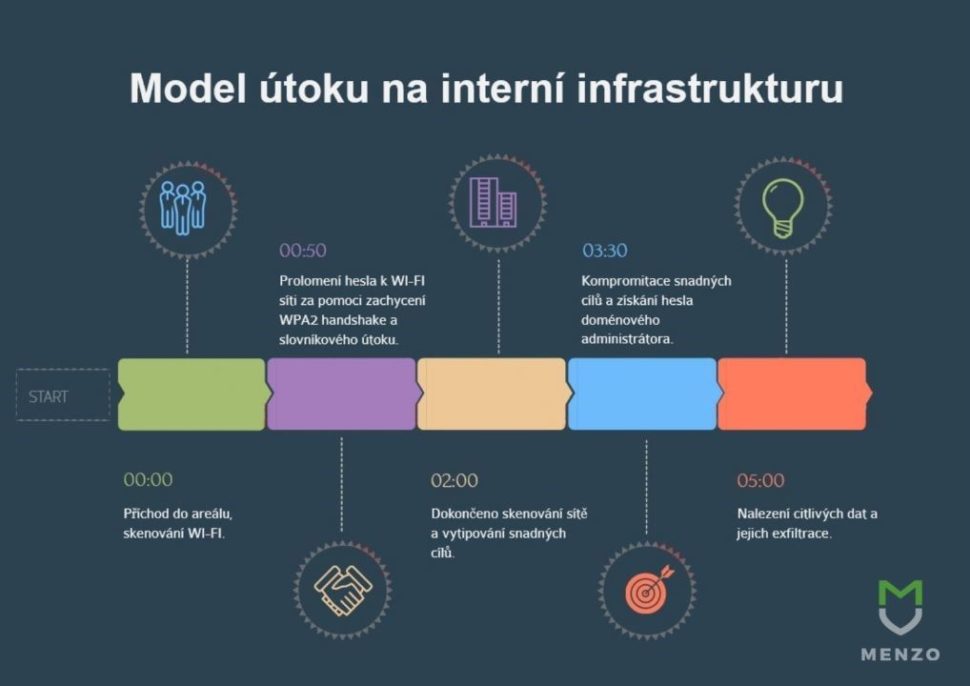
Take a look at the model of attacking the internal infrastructure directly at the client. This is how the penetration test took place in real time.
Co najdete ve výsledcích penetračních testů?
Celé testování shrneme do závěrečné zprávy s výčtem nálezů a s doporučeními na nápravu stavu. Naši specialisté vám vše objasní v prezentaci výsledků testování.
Prohlédněte si vybrané slidy z prezentací: